Imagine this secret online marketplace where stolen data is traded like any other commodity. This is the dark web, a hidden part of the Internet that regular search engines can’t reach. Here, hackers and cybercriminals can buy and sell everything from credit card details and social security numbers to confidential business documents and intellectual property.
Today, businesses need to watch out for the dark web. Even a single unnoticed data breach can expose sensitive customer information or confidential internal documents. Leaked data can end up on the dark web, putting your company at risk of financial loss, brand damage, and even compromised competitive advantages.
What is Dark Web Monitoring?
Dark web monitoring is a proactive cybersecurity tool that works like an early warning system. Some cybersecurity services offer dark web monitoring, which involves scanning thousands of websites for personal and business information that cybercriminals may be exploiting. Here’s how it works:
- Specialized Crawlers: Monitoring services deploy sophisticated software to search dark web forums, marketplaces, and chat rooms to find where people trade stolen data.
- Data Matching: They compare this information with your company’s data, such as employee email addresses, customer information, or intellectual property details.
- Alerts and Action: You’ll receive immediate notification if it finds any leaked data. This allows you to take swift action against the threats.
Dark web monitoring services will look for unauthorized use and distribution of sensitive information like:
- Email addresses
- Social security numbers
- Medical information
- Drivers licenses
- Login information
- Passwords
Surface Web, Deep Web, and Dark Web
Understanding the different layers of the web is essential to fully grasp the concept of dark web monitoring.
The web consists of three main groups: surface web, deep web, and dark web.
- Surface Web: Also known as the visible web, this is the easily accessible part of the Internet you encounter daily. Search engines like Google index this vast collection of websites, making information readily available through everyday browsing.
- Deep Web: Everything else that isn’t indexed by search engines. It exists on the Internet but is not accessible to the general public. For example, your Netflix account, online email, or bank account login credentials are part of the deep web. It’s not necessarily illegal content, just information that isn’t meant to be publicly available through a search.
- Dark web: This is a small part of the deep web. Accessing this hidden area requires special software and is often linked to criminal activities such as selling stolen data or hosting hacking forums. However, it can also serve legitimate purposes like enabling whistleblowing or anonymous communication.
Is the Dark Web Real?
Nobody knows when the dark web first emerged, but the term has been around for at least a decade. Most internet users will discover surface-level web content via search engines like Google. Since the dark web is hidden within the deep web, it’s not likely that a typical internet user will stumble upon it.
However, the dark web is real. You can access it through specialized software and networks, like Tor browsers. These browsers are designed specifically for the dark web, creating a solid barrier to entry that keeps the number of users relatively small.
Is the Dark Web Safe?
The Dark Web offers anonymity because it uses encrypted connections. When you access it, you’re not connecting to servers you typically find through search engines. All data that travels through this network stays within it, providing security and privacy.
But here’s the catch: this anonymity cuts both ways. Publishers and users remain anonymous on the Dark Web, making it a free-for-all with no rules. This creates a haven for criminals to share information and exploit stolen data. They can also develop new ways to steal your information or bypass security measures.
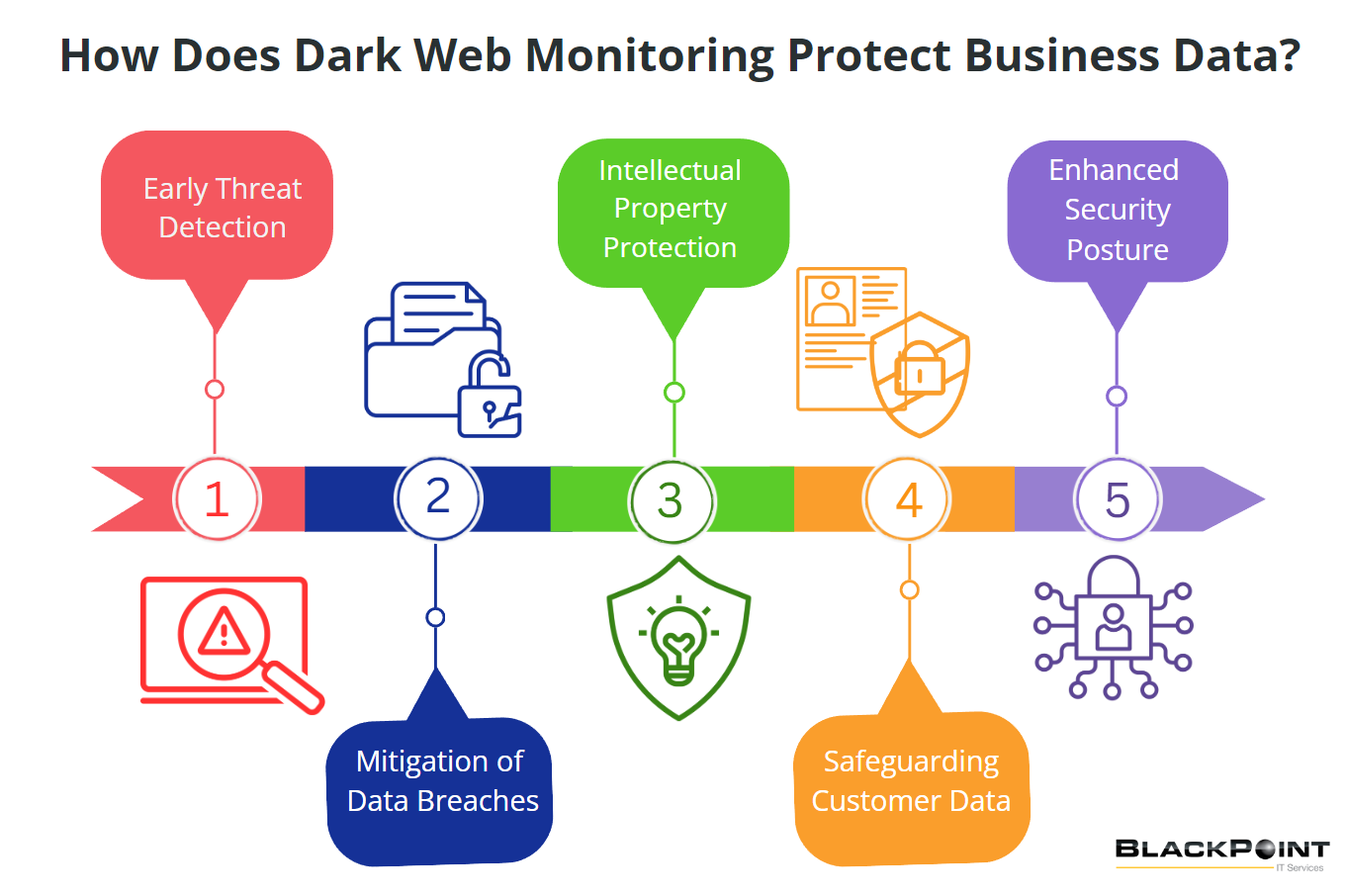
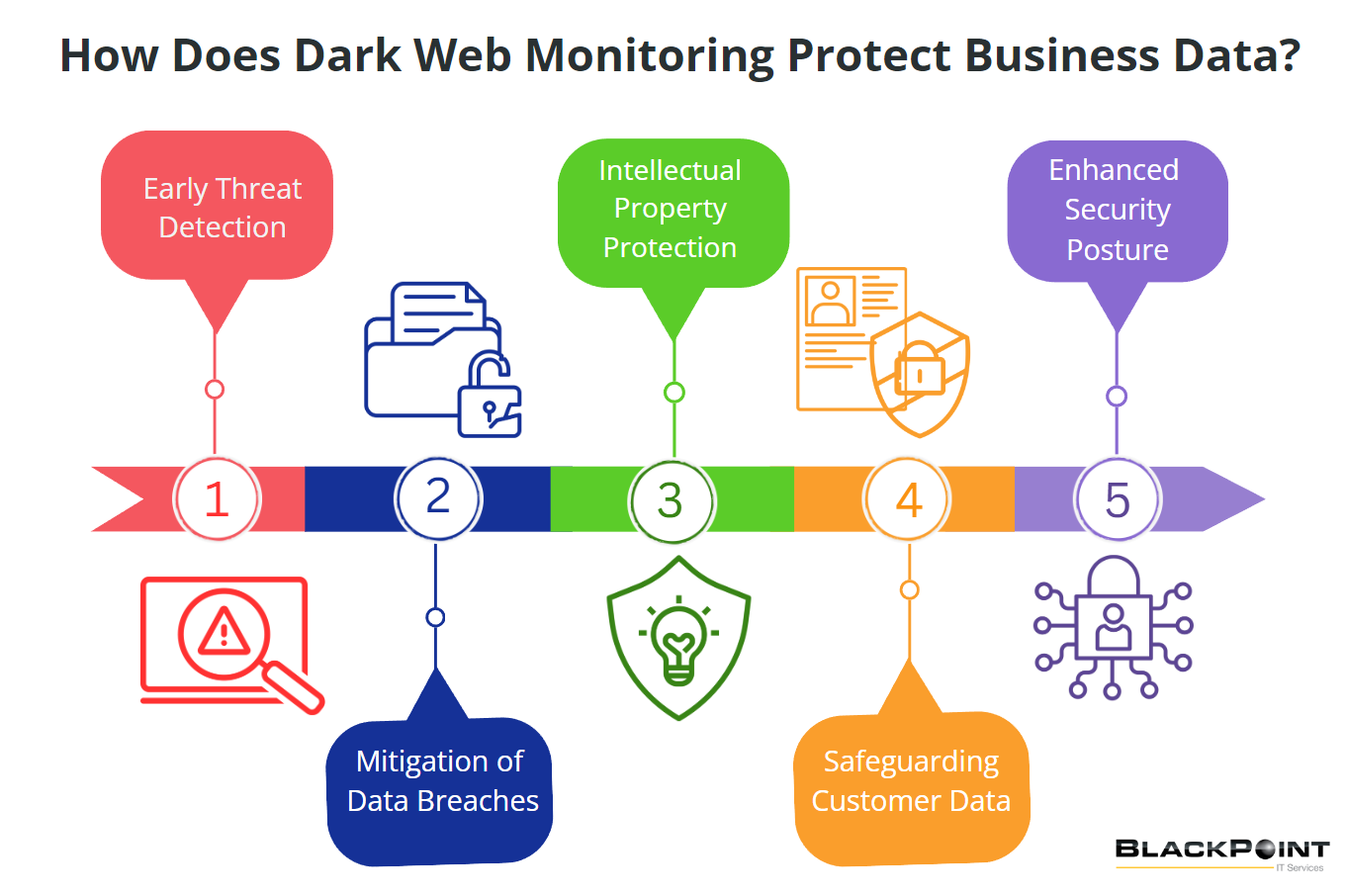
How Does Dark Web Monitoring Protect Business Data?
- Early Threat Detection: Dark web monitoring involves continuous surveillance of the dark web to spot anyone trading or selling your company’s data illegally. This way, you catch threats early before they turn into full-blown attacks.
- Mitigation of Data Breaches: If your sensitive data ends up on the dark web, dark web monitoring helps you act fast to reduce the damage. You can quickly change passwords, add extra security measures, and notify affected parties to prevent further issues.
- Protection of Intellectual Property: Protecting your intellectual property (IP) is crucial for any business. Dark web monitoring acts like a guard, alerting you if someone is trying to sell your confidential documents or trade secrets. With this early warning system, you can quickly take action to safeguard your innovations and strategies. By stopping competitors or malicious actors from exploiting your valuable IP, you maintain your competitive edge and protect your business’s future.
- Safeguarding Customer Data: Customer trust is the foundation of any business. A breach exposing sensitive information like credit card details or personal data can be devastating. Protecting customer data can maintain your reputation and avoid potential legal issues.
- Enhanced Security Posture: Adding dark web monitoring to your cybersecurity strategy can strengthen your overall security. You’ll gain valuable insights into new threats and vulnerabilities, helping you stay ahead of cybercriminals and proactively address weaknesses.
Benefits of Dark Web Monitoring for Businesses
- Proactive Risk Management: Dark web monitoring helps you manage risks by spotting potential threats before they can cause harm. This proactive approach is far more effective than reactive measures taken after an incident has occurred.
- Cost Savings: Data breaches are a nightmare—legal fees, fines, and reputational damage can seriously dent your business. Dark web monitoring can help you avoid these costs by preventing such incidents from happening.
- Improved Incident Response: With Dark Web monitoring, you can improve your incident response times. Early detection allows you to respond swiftly to threats, minimizing the potential damage and recovery time.
At BlackPoint IT Services, we understand that threats are becoming more advanced and dangerous. That’s why we have taken steps to ensure that our clients are equipped with the best strategies to combat cybercriminals. We also offer a free cybersecurity assessment. The best way to avoid becoming tomorrow’s headline for the latest cyberattack is to have a strong offense. Get ready with BlackPoint IT.